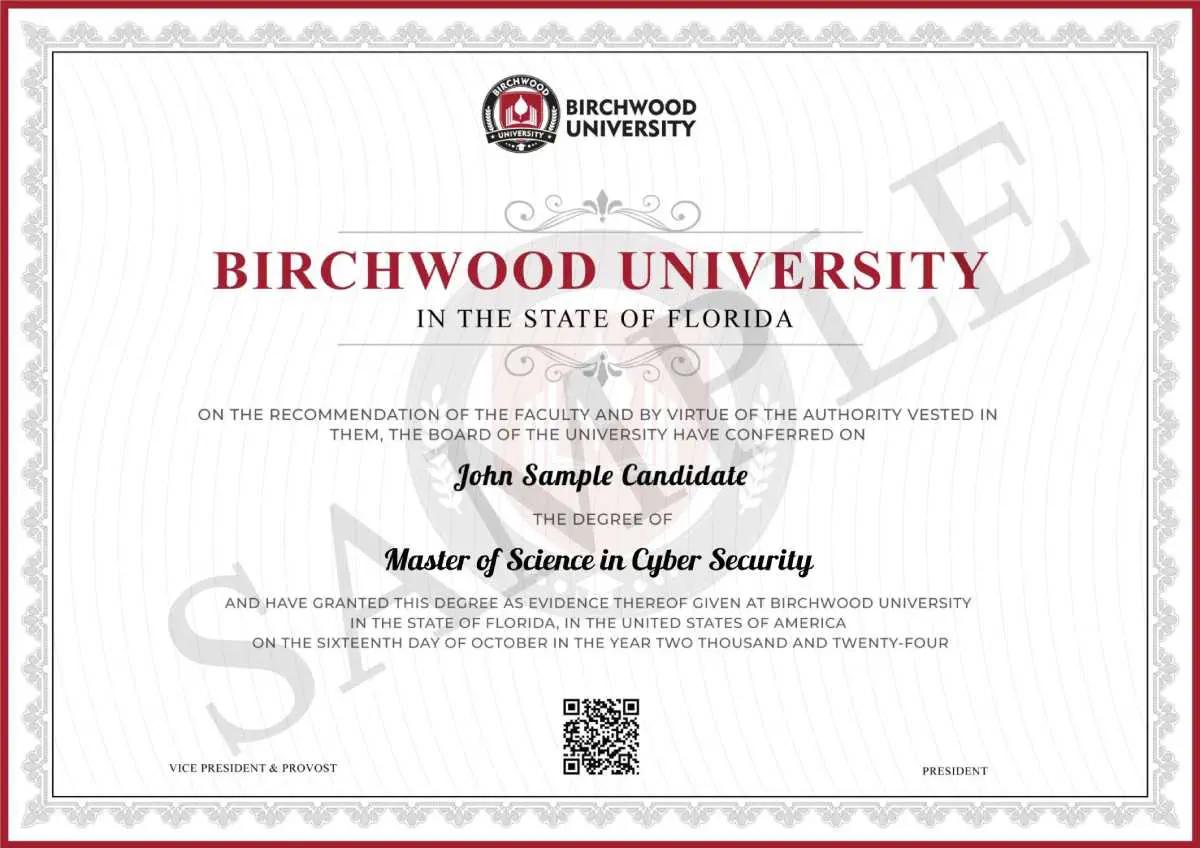
Master of Science in Cyber Security
Master of Science in Cyber Security
For help, give us a call:+1 (407) 815-7366

The Cyber Security Landscape
Why choose a Master of Science in Cyber Security?
Master of Science in Cyber Security is a professional degree program designed to prepare students for careers in the field of cyber security. It typically combines technical skills from the field of computer science with policy, law, ethics, and business to provide students with the knowledge and skills necessary to protect organizations from cyber threats. Courses cover topics such as network security, digital forensics, information security management, cyber law, cryptography, and secure software engineering. With the increasing demand for cyber security professionals, a Master of Science in Cyber Security can open doors to a wide variety of exciting job opportunities in the rapidly evolving field.
What does this course have to offer?
Explore key learning outcomes, skills, and competencies designed to shape future professionals.
- Apply foundational networking concepts, protocols, and architectures to support secure data communication systems.
- Configure and manage Linux-based environments, particularly Kali Linux, for security testing and system administration.
- Analyze cybersecurity threats and vulnerabilities using ethical hacking methodologies and penetration testing tools.
- Evaluate various cyberattack techniques and implement appropriate countermeasures to safeguard data systems.
- Apply cryptographic principles and IoT security frameworks to protect data across distributed and connected environments.
- Conduct digital forensic investigations to collect, analyze, and preserve electronic evidence.
- Integrate cybersecurity practices into data science workflows to ensure secure, compliant, and resilient data-driven solutions.
Get Expert Academic Guidance Today
Connect with experienced advisors who understand your goals, offering personalised academic guidance, clear direction, and practical solutions to help you make confident decisions about your education and future.
.webp&w=2048&q=75)
.webp&w=2048&q=75)
Admission Requirements
General Admission Requirements
- A copy of a valid government-issued photo identity card.
- A copy of an updated resume.
- Any document if not in English must be accompanied by a certified translated copy.
Eligiblity Criteria For Master of Science in Cyber Security
- Submit a 500-word essay (minimum) summarizing the applicant’s interest in the Master of Science in Cyber Security program outlining your professional aspirations.
- Provide an official undergraduate degree transcript verifying the completion of a bachelor’s degree in computer science, engineering, information technology, or a related field with a cumulative GPA of 2.5 or higher.
- Provide two (2) professional recommendation letters attesting to your academic abilities and professional potential.
- Personal Interviews will be conducted with the Director of Education for applicants with a GPA below 2.5.
Your Path to Admission
We evaluate candidates based on their educational background, professional performance, consideration, and openness to applications. Our goal is to identify motivated individuals with strong leadership potential and a passion for advancing in the field of cyber security.
Step 1
Online Application
Step 2
Online Assessment
Step 3
Personal Interview
Step 4
Documents Verification
Step 5
Final Committee Decision


Graduation Requirements
Application For Admission
All individuals interested in applying for admission to the university must complete an application and submit a non-refundable registration fee of $150.00 (payable by check, money order, or credit card). Checks and money orders should be made payable to Birchwood University.
Applicants must also provide all required application documents to be considered for admission. Once an admissions decision has been made, the candidate will receive an email with further instructions. Admissions agents will maintain regular contact with applicants to ensure all necessary documents are received by the admissions office.
Post Graduation Requirements
To graduate from Birchwood University and to receive a degree, the students must:
- Complete all credits as stated in the catalog.
- Need to earn a minimum cumulative grade point average of 3.0.
- Meet satisfactory academic progress.
- Fulfill all financial obligations.

Get in Touch Today
Contact our team for quick support and guidance. Get clear answers, understand your options, and take the next step in your academics with confidence and ease.
Master of Science in Cyber Security Course - Key Highlights
Earn a globally recognized online master's degree equally credible as offline.

Program Objectives
Upon completion of the program, students will
- Apply the necessary skills to protect a network or system from hacking.
- Apply theoretical knowledge in real life scenarios and perform hacking on different devices.
- Effectively use the skills to perform ethical hacking.
- Be proficient in different techniques used by the attackers to gain access to any device.
- Be proficient in the countermeasures for different techniques of hacking.
- Be proficient in analyzing and detecting security threats to an organization's computing systems.
- Be proficient in applying security principles and practices to maintain operations of computing systems in the presence of risks and threats.
- Effectively communicate across all levels of the organization to convey complex technical matters.
- Recognize professional responsibility to make informed decisions on computing practices based on legal and ethical principles.
Program Curriculum
A summary of the courses you will learn during the program.
MCS500 | Networking and Kali Linux | 3 Credit Hours
MCS505 | Networking Concept and Kali Linux | 3 Credit Hours
MCS510 | Kali Linux for Hacking | 3 Credit Hours
MCS515 | Concepts of Hacking | 3 Credit Hours
MCS520 | Engineering of Hacking | 3 Credit Hours
MCS525 | Internet of Things and Cryptography | 3 Credit Hours
MCS530 | Forensic Computing | 3 Credit Hours
MCS535 | Application And Device Control | 3 Credit Hours
MCS540 | Administration and Audits | 6 Credit Hours
MCS545 | Capstone Project | 6 Credit Hours
Faculty Members
Explore insights, research, and expert perspectives shared by our faculty at Birchwood University.

Prof.Tilokie Depoo, Ph.D

Dr. Andrew Salisbury
Dr. Andrew Salisbury is a veteran educator and academic from England, UK, who has an eclectic background in the fields of engineering, computer science, business, and digital change. He possesses a BEng (Hons) and a PhD from Lancaster University and has complemented his qualification with postgraduate awards in the teaching and learning course at Sheffield University, achieving Fellowships in Higher Education (FHEA and SFHEA). His teaching portfolio consists of data analytics, object-oriented programming, AI, and machine learning online courses at various universities like UCL, Open University, University of Leeds, University of Edinburgh, University of Aston, and University of Bolton. Dr. Salisbury's research interests are management information systems, database design, and digital transformation with emphasis on the embedding of technology into business education.

Dr. Vinícius Dezem
Dr. Vinícius Dezem is a Brazilian banking executive and data-driven financial solutions expert, strategic management, and financial technologies. He has a Ph.D. in Engineering Knowledge Management from the Federal University of Santa Catarina (UFSC), with an area of focus on Open Banking APIs and decision support systems. His Ph.D. thesis, entitled "Strategies for Future Data-Driven Banking by Open Banking APIs," explores best practices for incorporating in-house and outsourced technology innovation in open banking.
The research highlights the flexibility and cost-saving nature of hybrid models in addressing tight deadlines and budget limitations. Professionally, Dezem has more than a decade of experience in banking. He has been a Banking Manager at Caixa Econômica Federal since 2012, where he has managed projects in data-driven branch optimization, credit structuring, project financing, and strategic partnership development. His job includes mentoring teams and developing a culture of ongoing improvement to drive improved performance.

Prof.Aida Mehrad, Ph.D

Prof.Egla Mansi, MS

Prof.Millet T.De Guzman, Ph.D

Prof.Ajay Dhruv, Ph.D

Prof.Vijal Jain, Ph.D

Prof.Samip Dhakal, MS

Prof.Rohan Kumar Reddy, MS
Licensure & Associations
We maintain high standards through licensure and trusted associations with leading organizations.
Earn an Eminent Master of Science in Cyber Security Degree from
Birchwood University
Same Master as On campus
Receive the same world-class education and global recognition as on- campus masters without the need to relocate.
Globally recognized US Degree
Birchwood University is licensed by the Florida Commission for Independent Education, Florida Department of Education.
Lifetime Alumni Status
Join an alumni network of professionals with as many in key leadership roles spread all over the globe.
Get Your Degree Today
Achieve your academic goals with a recognised degree. Gain knowledge, build skills, and open new career opportunities with a qualification designed to support your growth and future success.
Additional Information for Master of Science in Cyber Security
Frequently Asked Questions
For quick answers, browse our Frequently Asked Questions on the website











